Harness the power of AI by generating simulated phishing emails to help bring awareness and identify the weakest links in your organization.
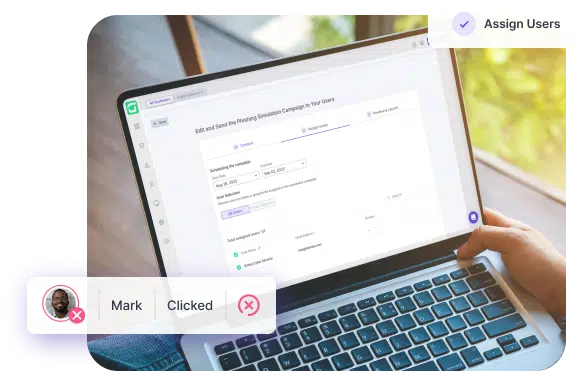



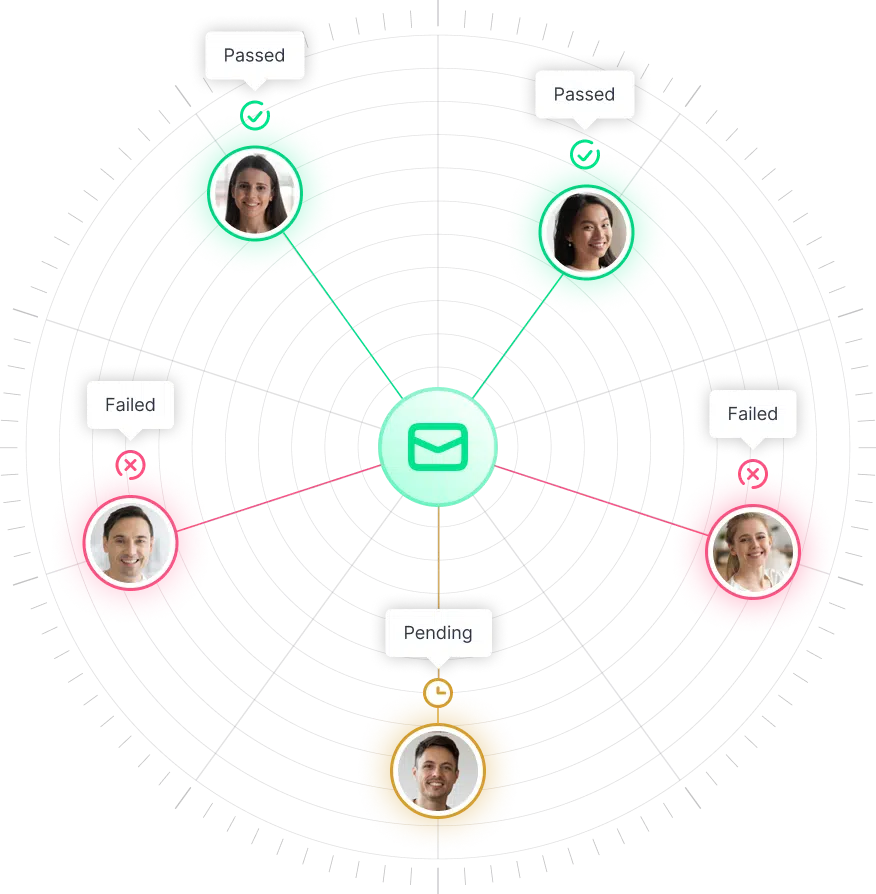
CTS Cyber Threat Security breaks the mold of traditional static libraries, providing dynamically tailored content for each department. This cutting-edge approach allows you to gather detailed data reports, highlighting the individuals who successfully identified the phishing attempts and those who failed to do so.
By staying up-to-date with the latest phishing trends, we ensure highly accurate simulations, arming your employees against emerging threats.
Email is widely used in business communication because of its organizational benefits, accessibility, authenticity, and privacy advantages. Nonetheless, its popularity also makes it an appealing target for cyber criminals.
Malware is any program or code designed to harm or exploit computer systems, including viruses, worms, Trojans, and other types of malicious software.
90% of cyberattacks originate
from phishing attempts
See in real-time the interactivity between employees and the simulation and gain insight into who passed and who failed
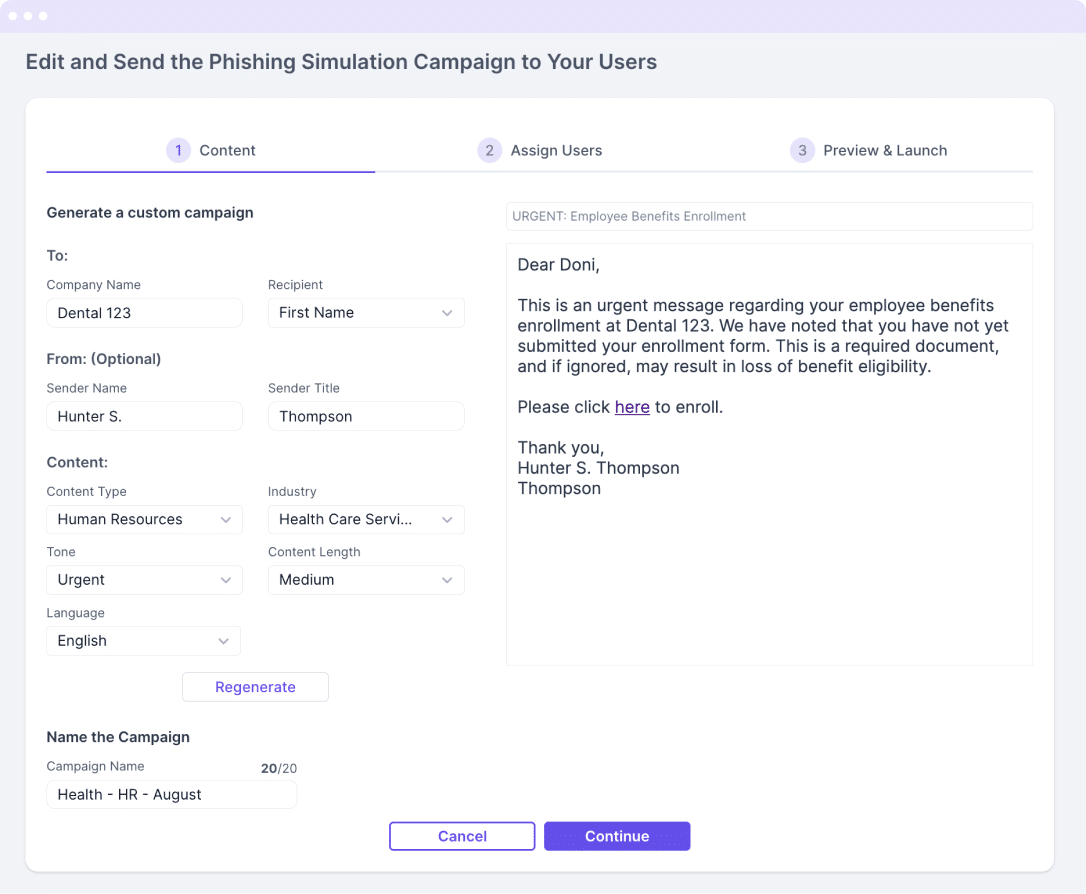
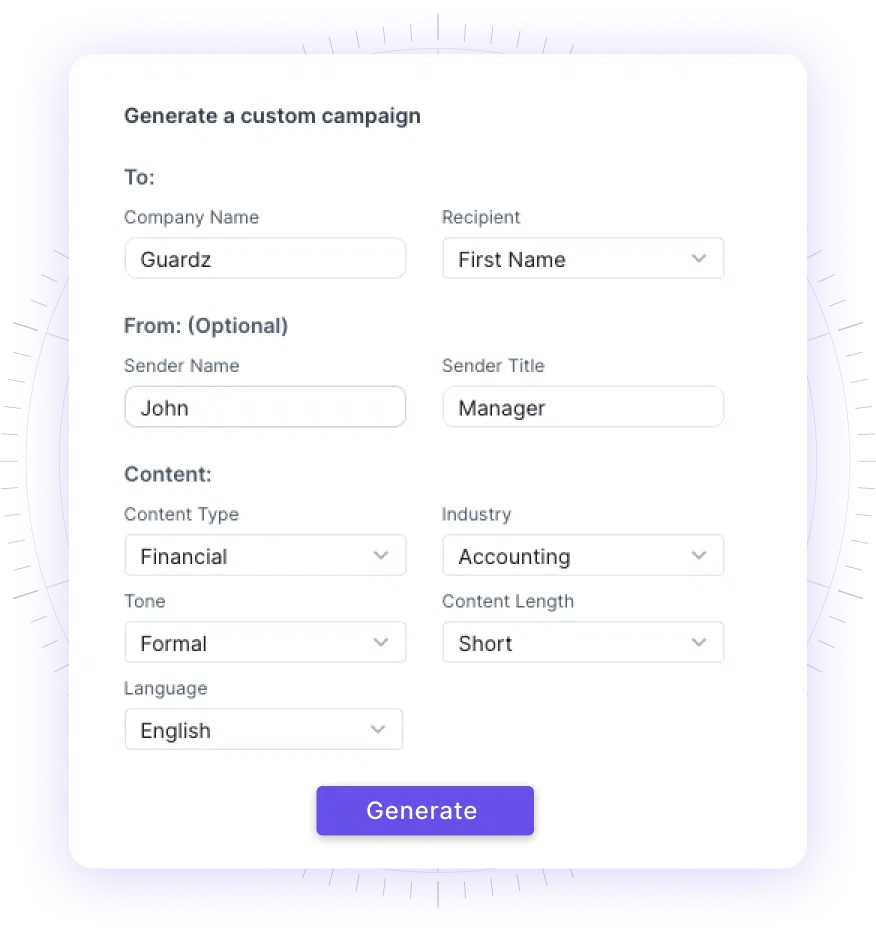
AI generates within a few seconds a personalized email template to be sent as part of the simulation using the values you’ve added. You can re-generate the content until you find the version you like.


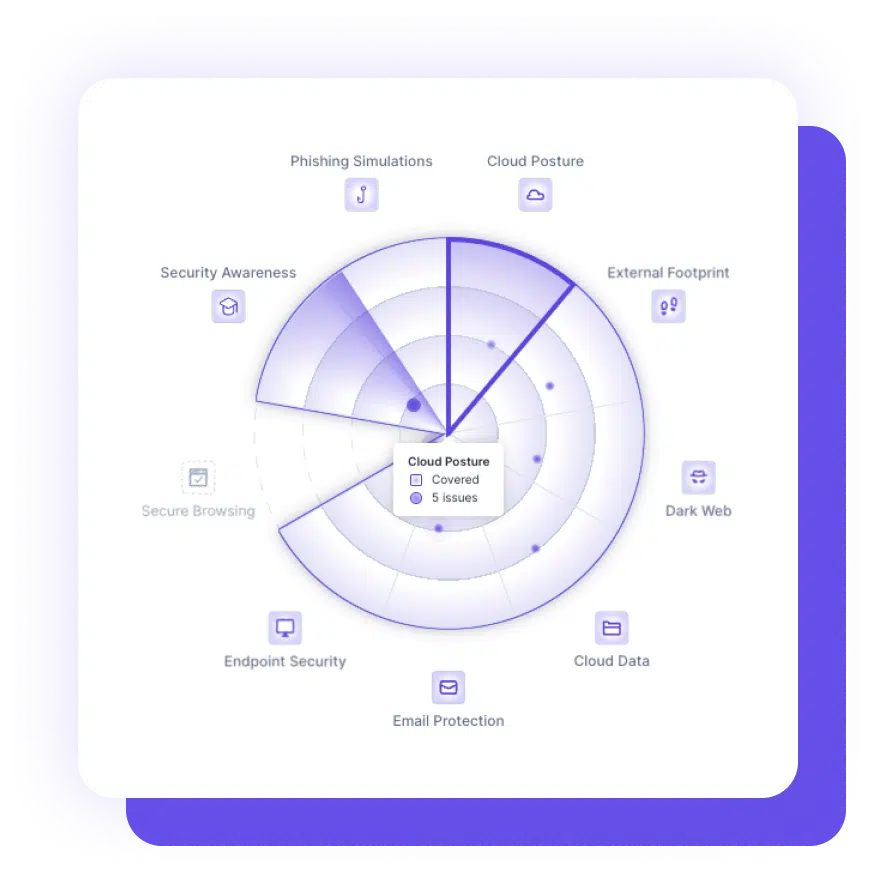
Centrally navigate the security of multiple clients, each with their unique environments and potential attack vectors, from a single platform, ensuring efficiency, better visibility, and consistency when securing your clients’ systems and data.
With one-click remediation and powerful integrations, even non-security experts can swiftly respond to cyber events.